𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧 𝐓𝐫𝐢𝐚𝐧𝐠𝐮𝐥𝐚𝐭𝐢𝐨𝐧: Unraveling the Most Advanced iPhone Attack that used four 0-day vulnerabilities
Security researchers at Kaspersky reveal the intricacies of “Operation Triangulation,” on Dec 27th, 2023, at the Chaos Communication Congress.
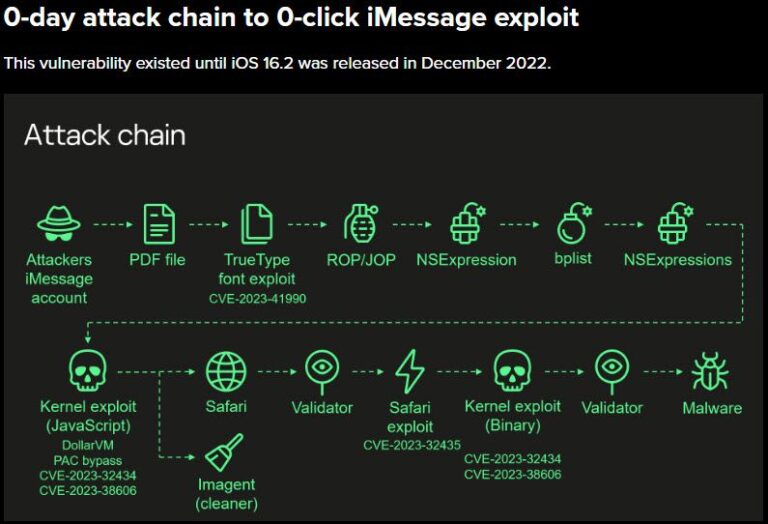
So why is this important? This was an extremely sophisticated iMessage vulnerability spanning from 2019 to December 2022. The attack chain, which has been labeled the “most sophisticated” ever seen, utilized four 0-day vulnerabilities, including a Pegasus 0-click iMessage exploit.
𝐵𝑒𝑓𝑜𝑟𝑒 𝑤𝑒 𝑑𝑖𝑣𝑒 𝑖𝑛𝑡𝑜 𝑡ℎ𝑒 𝑑𝑒𝑡𝑎𝑖𝑙𝑠, 𝐼 𝑤𝑜𝑢𝑙𝑑 𝑙𝑖𝑘𝑒 𝑡𝑜 𝑠𝑎𝑦 𝑡ℎ𝑎𝑡 𝑡ℎ𝑖𝑠 𝑖𝑃ℎ𝑜𝑛𝑒 𝑎𝑡𝑡𝑎𝑐𝑘 𝑢𝑛𝑑𝑒𝑟𝑠𝑐𝑜𝑟𝑒𝑠 𝑎𝑛 𝑎𝑙𝑎𝑟𝑚𝑖𝑛𝑔 𝑙𝑒𝑣𝑒𝑙 𝑜𝑓 𝑠𝑜𝑝ℎ𝑖𝑠𝑡𝑖𝑐𝑎𝑡𝑖𝑜𝑛 𝑤𝑖𝑡ℎ 4 𝑧𝑒𝑟𝑜-𝑑𝑎𝑦𝑠. 𝑇ℎ𝑒 𝑚𝑦𝑠𝑡𝑒𝑟𝑦 𝑠𝑢𝑟𝑟𝑜𝑢𝑛𝑑𝑖𝑛𝑔 𝐶𝑉𝐸-2023-38606 𝑒𝑚𝑝ℎ𝑎𝑠𝑖𝑧𝑒𝑠 𝑡ℎ𝑒 𝑛𝑒𝑒𝑑 𝑓𝑜𝑟 𝑟𝑜𝑏𝑢𝑠𝑡 𝑐𝑦𝑏𝑒𝑟𝑠𝑒𝑐𝑢𝑟𝑖𝑡𝑦. 𝐼𝑛𝑡𝑒𝑔𝑟𝑎𝑡𝑖𝑛𝑔 𝐴𝐼 𝑖𝑛𝑡𝑜 𝑠𝑢𝑐ℎ 𝑒𝑥𝑝𝑙𝑜𝑖𝑡𝑠 𝑤𝑖𝑙𝑙 𝑜𝑛𝑙𝑦 𝑎𝑚𝑝𝑙𝑖𝑓𝑦 𝑡ℎ𝑟𝑒𝑎𝑡𝑠, 𝑟𝑒𝑞𝑢𝑖𝑟𝑖𝑛𝑔 𝑣𝑖𝑔𝑖𝑙𝑎𝑛𝑡 𝐴𝐼 𝑑𝑒𝑓𝑒𝑛𝑠𝑒𝑠, 𝑡𝑜 𝑏𝑒 𝑐𝑟𝑒𝑎𝑡𝑒𝑑.
In the current world where Generative AI can pentest systems, and move faster than a human can react. “𝗦𝘆𝘀𝘁𝗲𝗺𝘀 𝘁𝗵𝗮𝘁 𝗿𝗲𝗹𝘆 𝗼𝗻 𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝘁𝗵𝗿𝗼𝘂𝗴𝗵 𝗼𝗯𝘀𝗰𝘂𝗿𝗶𝘁𝘆 𝗰𝗮𝗻 𝗻𝗲𝘃𝗲𝗿 𝗯𝗲 𝘁𝗿𝘂𝗹𝘆 𝘀𝗲𝗰𝘂𝗿𝗲.”
Just to be clear although I am talking about AI above. This finding was before GenAI took off. My goal is to bring awareness to this now so that security teams start fighting AI with AI.
—– Back to the post —–
𝐊𝐞𝐲 𝐏𝐨𝐢𝐧𝐭𝐬:
🔹 Attackers exploited a remote code execution vulnerability (CVE-2023-41990) in Apple’s ADJUST TrueType font instruction, remaining undetected by users.
🔹 The attack involved return/jump-oriented programming, multiple stages, and an obfuscated JavaScript exploit with around 11,000 lines of code.
Vulnerabilities in XNU’s memory mapping syscalls (CVE-2023-32434) and hardware memory-mapped I/O registers were crucial in obtaining read/write access to the device’s entire physical memory.
🔹 The attack chain concluded with the exploitation of CVE-2023-32435 through a Safari exploit, executing a shellcode and obtaining root privileges for loading spyware.
🔹 Researchers emphasize the mystery surrounding CVE-2023-38606 and invite iOS security researchers to contribute insights, highlighting the insecurity of systems relying on “security through obscurity.”
The researchers plan to delve deeper into each vulnerability in 2024.
#Cybersecurity #ai #security #zerotrust #ciso #infosec #genai VOCAL Council Theia Institute Peer Insights Gartner InsightJam.com Bot Nirvana
𝗡𝗼𝘁𝗶𝗰𝗲: The views expressed in this post are my own. The views within any of my posts or articles are not those of my employer or the employers of any contributing experts. 𝗟𝗶𝗸𝗲 👍 this post? Click 𝘁𝗵𝗲 𝗯𝗲𝗹𝗹 icon 🔔 for more!
for more!